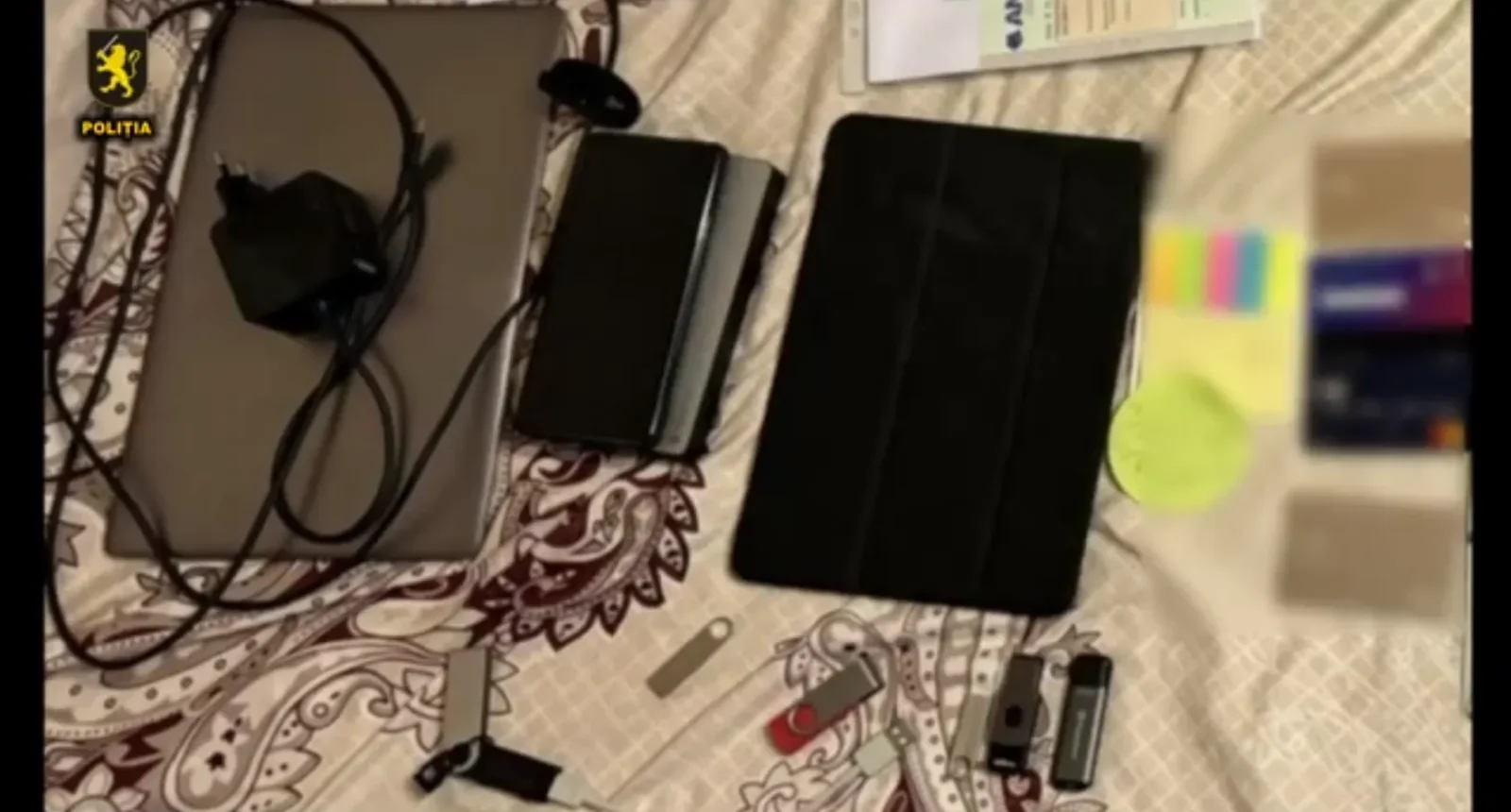
Last week, Moldovan authorities arrested a suspect connected to a spate of ransomware attacks in the Netherlands in 2021. During the arrest police seized an electronic wallet likely containing cryptocurrency, multiple laptops and mobile devices, and around 80,000 euros (89,383 USD) in cash.
Although this arrest took place four years after the initial incidents, it raises a glimmer of hope in the often pessimistic world of ransomware policy – such cyber criminals are usually thought to be simply out of reach of law enforcement. Such law enforcement actions are more regular than often appreciated. However, they can only be truly successful in the context of a holistic counter-ransomware policy that protects the most vulnerable organisations.
Ransomware in the Netherlands
Like most digitally saturated countries, the Netherlands faces a thorny ransomware problem. Along with hostile state actors, cybercriminals using ransomware and other forms of digital extortion are afforded extensive discussion in the 2024 Dutch national cybersecurity assessment. This assessment records 140 to 180 ransomware incidents in the Netherlands in 2023, with discrepancies partly due to reporting processes: higher numbers come from the Dutch data protection authority, where reporting data breaches is mandatory under the EU’s General Data Protection Regulation (GDPR). Lower numbers come from other data collection efforts without a legal mandate to collect reports, which also impose an arbitrary size threshold excluding small organisations (100 or fewer full-time employees). The actual number of ransomware incidents, especially those affecting small- and medium-sized enterprises and other local entities, is likely to be far higher.
Recent ransomware incidents have caused organisations and their customers to suffer business disruptions, lose data, and incur high remediation costs. A notable incident affecting a maritime services provider forced them to adopt emergency measures on oil rigs and conduct physical supervision of drilling. But ransomware incidents have also had impacts closer to home. In 2023, ransomware attacks in the Netherlands affected healthcare and elderly care providers, with the latter incident temporarily disabling emergency buttons for elderly patients.
The incidents leading to the recent Moldova arrest involved a ransomware strain known as ‘DoppelPaymer’, which was used most frequently between 2019 and 2021. The cybercriminals behind DoppelPaymer sometimes used aggressive tactics to coerce victims into paying, going so far as to call individuals at victim companies and threaten to turn up at their homes and call their relatives. DoppelPaymer was responsible for serious incidents across several countries, including an attack on a German hospital that may have contributed to a patient’s death.
The most notable DoppelPaymer incident in the Netherlands targeted the Dutch Research Council (NWO) in March 2021. Key servers were compromised and the NWO’s network had to be taken offline. Grant application rounds were suspended mid-stream, email systems went dark, and two affiliated research bodies were also impacted. The NWO attributed this incident to DoppelPaymer and publicly refused to pay any ransom, a stance that led the DoppelPaymer attackers to publish stolen internal documents on the internet. It took weeks for NWO to restore operations, delaying research funding for scientists across the country.
The tricky problem of ransomware countermeasures
Law enforcement have attempted to disrupt those behind DoppelPaymer before. In February 2023, German and Ukrainian police simultaneously raided the houses of suspected DoppelPaymer cybercriminals in both countries, with follow-up actions later that year. These interventions appeared to be more aimed at finding and prosecuting those responsible rather than active disruption – the DoppelPaymer leak site was only active until March 2021. The law enforcement action in Moldova this week seems to follow a similar logic.
However, even though DoppelPaymer disappeared, we cannot be sure that the people responsible for it ceased their activity. Ransomware groups frequently change names, branding, tactics and technical infrastructure to stay ahead of law enforcement.
One key aspect of the Moldova arrests is international cooperation, with the press release proudly emphasising ‘operative information and effective cooperation’ between Moldova and the Netherlands (as well as domestic cooperation between the Moldovan Center for Combating Cybercrimes and the National Investigation Inspectorate). Given that ransomware operators are usually spread across multiple countries, and are rarely located in the same country as victims, international cooperation – including through Europol and Interpol– are crucial to effective response.
Despite the many difficulties involved, high-profile actions like arrests happen regularly – if not frequently. The Ransomware Countermeasures Tracker, developed by Virtual Routes (Binding Hook’s parent organisation), includes 38 instances of arrests worldwide since 2010, peaking in 2021 with 15 arrests that year. The Netherlands has contributed to 7 arrest operations, of a total of 32 anti-ransomware interventions since 2015. Moldova, on the other hand, had previously only played a small part in an Interpol takedown operation with over 50 countries participating, suggesting that this is a major step forward for countering ransomware in Moldova.
Post-incident measures can only go so far
Law enforcement operations to track down cybercriminals are crucial to restoring justice – especially where, as in the Moldova case, extradition procedures have already been started to take the suspect to the Netherlands. These operations also contribute to deterrence, as cybercriminals may be less likely to engage in ransomware if they might be arrested and extradited while travelling or even arrested in their home countries.
However, effectively combating ransomware also requires pre-emptive action, from takedowns of cybercriminal infrastructure to the often mooted and always controversial topics of payment bans and cyber insurance. Here, smaller organisations – SMEs, nonprofits, and other local community groups – are often left out of ransomware policy discussions.
At Virtual Routes, we have now extended the Google.org Cybersecurity Seminars program to the Netherlands, to enable university students to help local community organisations defend against ransomware attacks. Over the coming two years, students will gain both practical skills and a deeper understanding of the broader implications of ransomware. Students will work with local community organisations on projects such as phishing simulations, tabletop incident response exercises, decryptor library development and victim support sheets, and network scanning to identify vulnerabilities. Together, these efforts will help to better secure under-resourced and highly vulnerable local communities in the Netherlands against ransomware, while providing practical experience to tomorrow’s cybersecurity professionals.